Nowadays, cyber attacks have become more and more frequent and your company could be the next to suffer one.
To best defend yourself, you need to take a proactive approach, identifying in time the signs of attack against your company.
Here are the 5 signs that you can tell if your company is about to suffer a cyber attack:
- Your system is slowing down
If you notice that your systems are not working as efficiently as usual and that the Internet is connecting intermittently, it could be a sign that you are experiencing a DoS (Denial of Service) attack. This is a type of attack that aims to destroy your server until it is completely unusable.
- Using an old operating system
Using an old operating system (OS), such as Windows 7, can put your business at risk as they are no longer supported by their developers.
This means that bugs or other problems will no longer be fixed, creating vulnerabilities that cybercriminals can take advantage of.
In addition, using older operating systems may also lead to incompatibility problems. You will not be able to use software that can only be run on newer operating systems.
- No IT security training
One of the most common causes of IT security problems is human error. For example, when one of your employees accidentally clicks on a dangerous link in a phishing e-mail.
This situation can easily be avoided if your company provides adequate IT security training to all employees.
- Outdated antivirus software
Using outdated anti-virus software can significantly expose your company to huge risks. This is because malware and viruses are constantly evolving and outdated software may not have the necessary tools to deal with the latest viruses.
- Employee turnover
Employee turnover increases the risk of cyber attacks. The departing employee may not adequately train the person taking his or her place on security procedures.
In addition, employees who have now left the company may remain aware of important passwords for your accounts, for example saved on their computers. This allows them to damage your company even if they no longer work there, or put it at risk if their computers are hacked.
- No adequate data backup
Creating backups for your business data is an essential activity as you ensure the recovery of any files should something unwanted happen, such as a cyber attack. Not having a constant data backup makes you an easy victim for ransomware attacks and blackmail by cybercriminals.
Having an adequate defence to protect against cyber attacks is the most effective way to avoid huge economic damage.
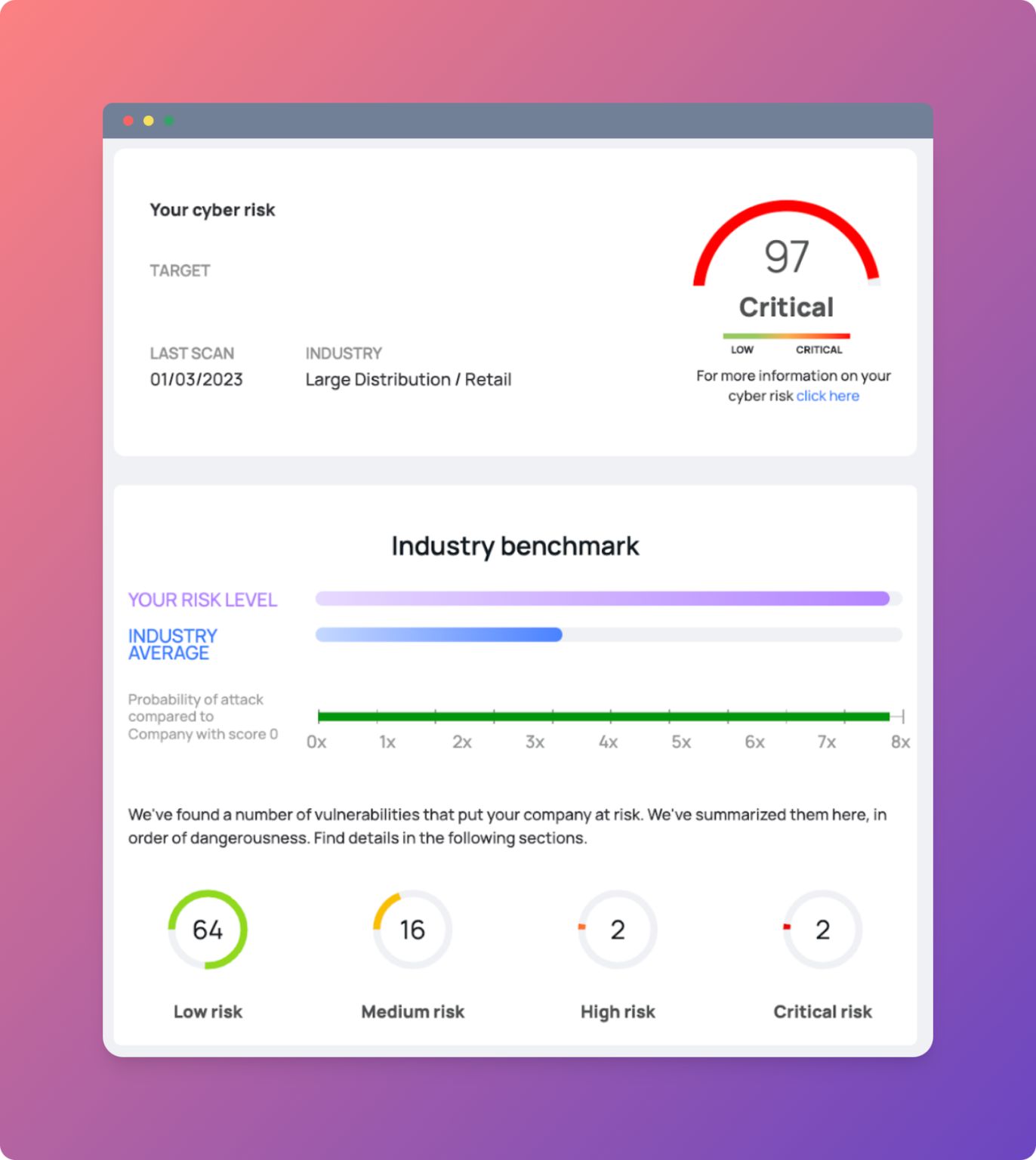
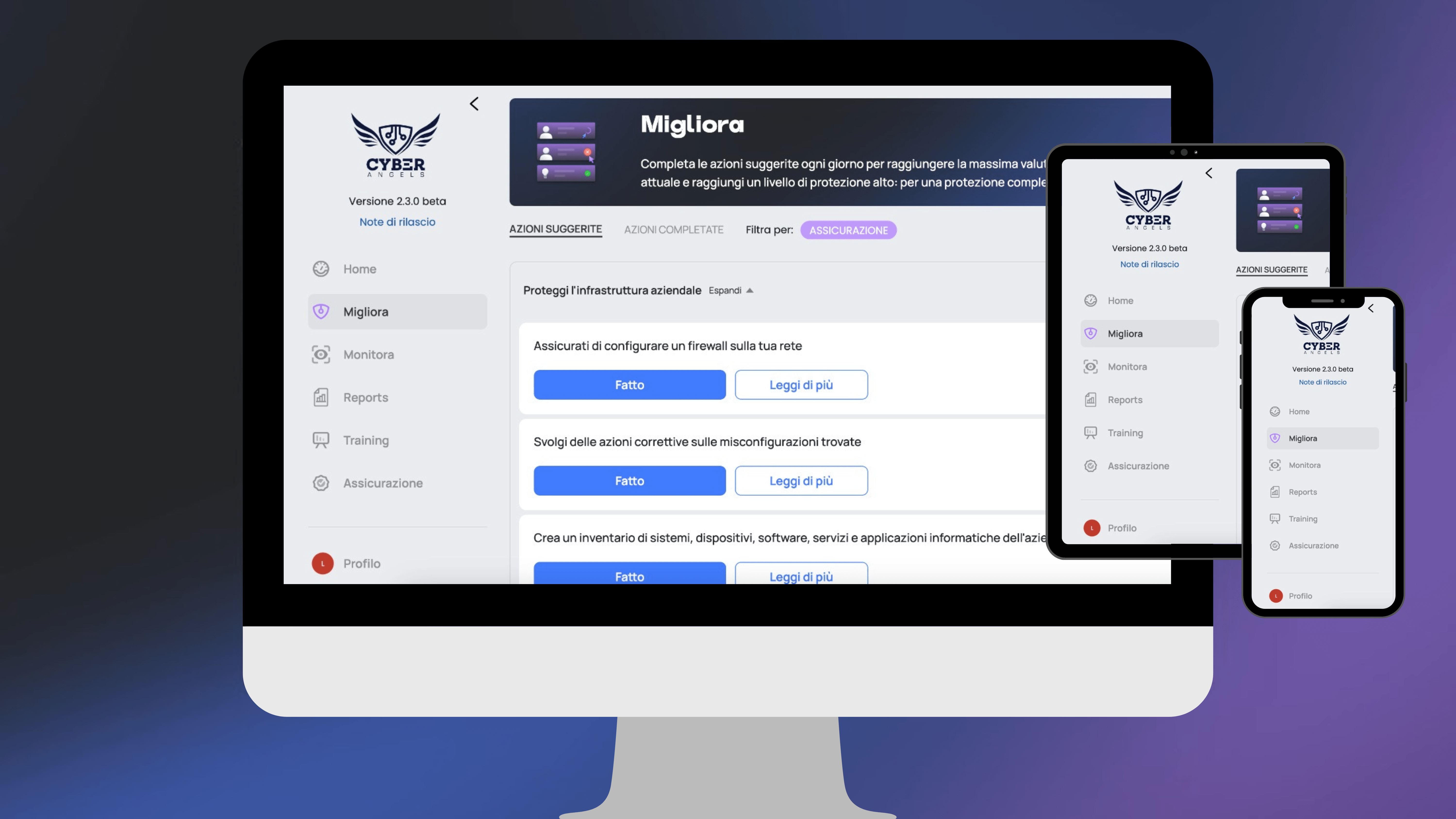
To protect yourself and insure against cyber damage, register for free on our platform and assess your company's cyber security for free