Companies and individuals exchange over 300 billion e-mails every day. The importance and necessity of the use of e-mail in the working environment often leads to ignoring and underestimating the risks involved in its use.
The email represents a technology not easy to protect and, consequently, can be subject to violations, alterations and manipulations.
According to recent research by Chubb, over the five-year period 2016-2020, cybercriminals have Stolen more than $28 billion through e-mail fraud. The average economic damage of a cyber attack is $150,000.
HOW THEY ENTER YOUR E-MAIL
Email hacking schemes are constantly evolving. In the past, e-mail attacks took the form of sending malicious links with attached viruses.
Today, cybercriminals use more refined techniques than in the past.
No more attachments or files that would be easily detected by malware scanners. These are now social engineering attacks, aimed at altering the identity of a sender, intercepting important messages and sending fake, apparently authentic content.
These attacks can easily breach a company's security defences.
"With the high level of deception and manipulation involved in these attacks, email security requires a zero-trust approach."said the researchers. "For example, an email from your bank requesting payment information or login credentials should be considered suspicious until the information can be independently verified through another channel, such as a direct phone call.".
Companies that are victims of e-mail compromise must act quickly: "Given the motivation and ingenuity of cybercriminals, organisations should bear in mind that these frauds continue to increase as criminals adapt to the countermeasures implemented to counter them."concludes the report.
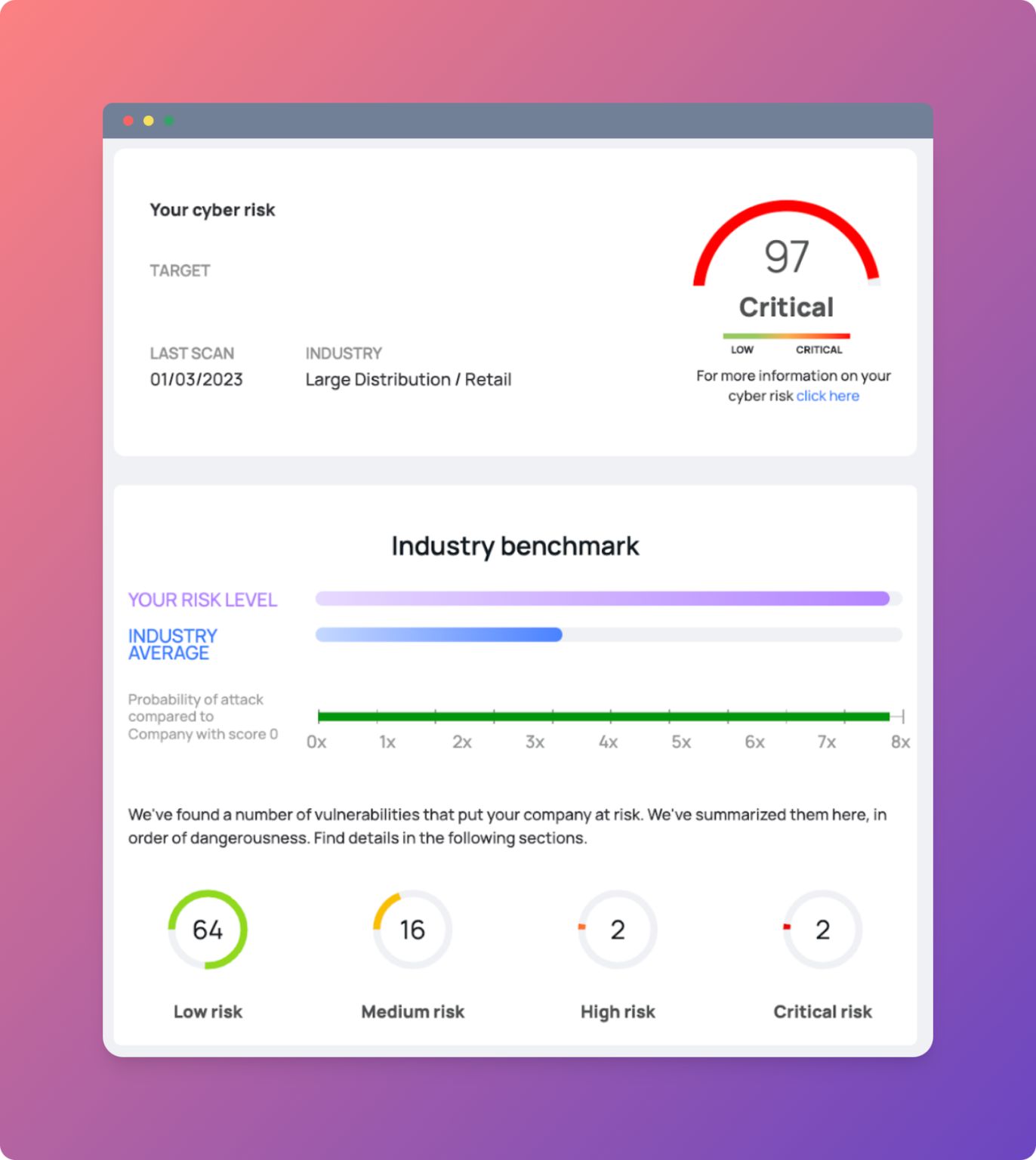
A careful analysis of the procedures used to verify electronically received information and an up-to-date cyber defence are essential requirements that an organisation must implement in order to counter social engineering fraud.
Cyber criminals will continue to act until companies adopt appropriate procedures to eliminate internal security vulnerabilities.
The only way to defend yourself, especially if you have a small or medium-sized business, is to prevent cyber attacks by identifying and eliminating your company's weaknesses.